 While I’ve never personally worked in the IT field, I have a number of friends who have, and I can appreciate their efforts to keep a network secure and functioning well. Sometimes, though, the cost of network security can be pretty annoying.
While I’ve never personally worked in the IT field, I have a number of friends who have, and I can appreciate their efforts to keep a network secure and functioning well. Sometimes, though, the cost of network security can be pretty annoying.
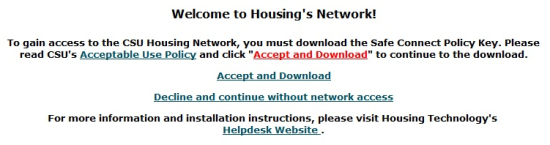
The university where I work is home to a top-notch group of IT guys that keep the wheels greased for over 15,000 network users. Just like many other universities, the IT department instituted a network authentication system to do several things, one of which being to cut down on illegal filesharing. This system included user login and a horrible little program called SafeConnect by Impulse.
Put simply, SafeConnect is a watchdog program that is forcibly installed on your system before you are allowed Internet access. It monitors to see that you have anti-virus software installed that is up to date, keeps tabs on your device preferences, and (as far as I can tell) was specifically designed to be a major pain in the butt.
If you’re like me, you probably don’t like to be forced to download third-party software. Also, if you’re like me, you probably don’t want to have your name associated with everything you do online. Finally, if you’re like me, you probably have an e-deathwish and don’t care what happens to your e-career when you do e-stupid things. Luckily, there are ways to avoid both SafeConnect and network authentication at many universities, and possibly fulfill a deeply seated wish to get yourself expelled.
Disclaimer: You probably know where this is going. Before you consider doing this for yourself, understand that while I performed these steps and survived to tell the story, my circumvention of the university network authentication system landed me in the Dean’s office for a rather eventful discussion with the Network Administrator present to see me squirm.
Step 1: Change your TCP/IP fingerprint
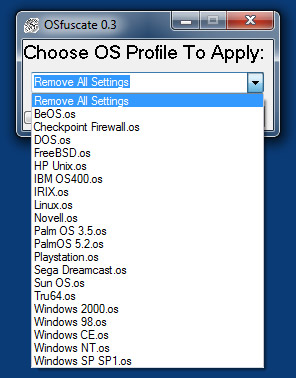
If you’re running Windows, your computer will be detected by the network as a valid candidate for SafeConnect. Fortunately, there is not a Linux-friendly version of the software. Changing the TCP/IP fingerprint will allow your computer to be detected as a Linux box and you can avoid that pesky download forever. You can achieve this manually by digging into the guts of your registry…or take a much easier route of using a nifty piece of software called OSfuscate.
Step 2 (optional): Change your MAC address
MAC addresses are hardwired into the network adaptor of your computer and are often used to filter rogue computers from a network. Spoofing a fake MAC address is not very difficult, and there are easy-to-follow tutorials here and here. I mark this step as optional because it is not essential for circumventing login. However, if you plan to do anything nefarious on a network, it’s best not to get an authentic MAC address banned from use.

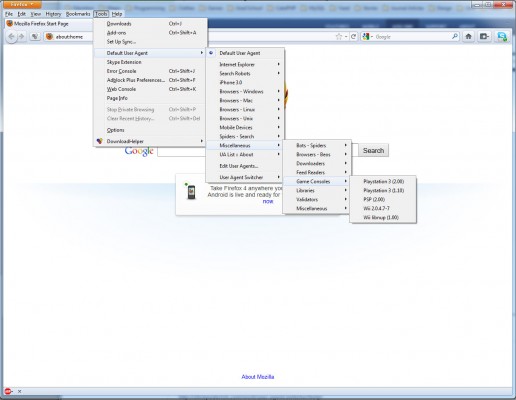
Step 3: Change your Browser User-Agent
At this point, if you’ve changed your TCP/IP fingerprint and uninstalled SafeConnect, firing up a browser should give you a typical network login screen. The interesting thing about most university networks is that they typically don’t require authentication of gaming consoles like a Playstation 3. If your university is anything like mine, its second tier of authentication (after SafeConnect) is identifying the User-Agent of the browser in use. If it detects a game console, it lets it pass through without authentication.
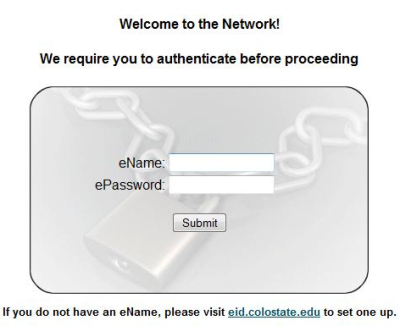
Spoofing a user-agent on a browser can be fairly easily accomplished with a Firefox plug-in or by modifying your desktop shortcut to Chrome.
Once your user-agent is spoofed, it is likely that you can now do anything online… semi-anonymously.
Step 4: Get discovered, deal with consequences
So, as the saying goes, all good things must come to an end. You see, network admins have a nose for this kind of behavior, and while I don’t know the specific tools that are used to detect it, you will eventually get caught. Chances are also quite good that circumventing network authentication is against your Student Code of Conduct.
In the end, this is a good exercise for those interested in network security, but a poor long-term defense against doing naughty things online.
Kids, keep your noses clean. SafeConnect and other forced software downloads may be lame, but risking expulsion to cover your e-tracks is just plain dumb.


Leave a Reply
You must be logged in to post a comment.